Docker 29.2.1 Release Notes: No CVEs Listed, Still Patch Fast
No CVEs listed. Patch anyway.
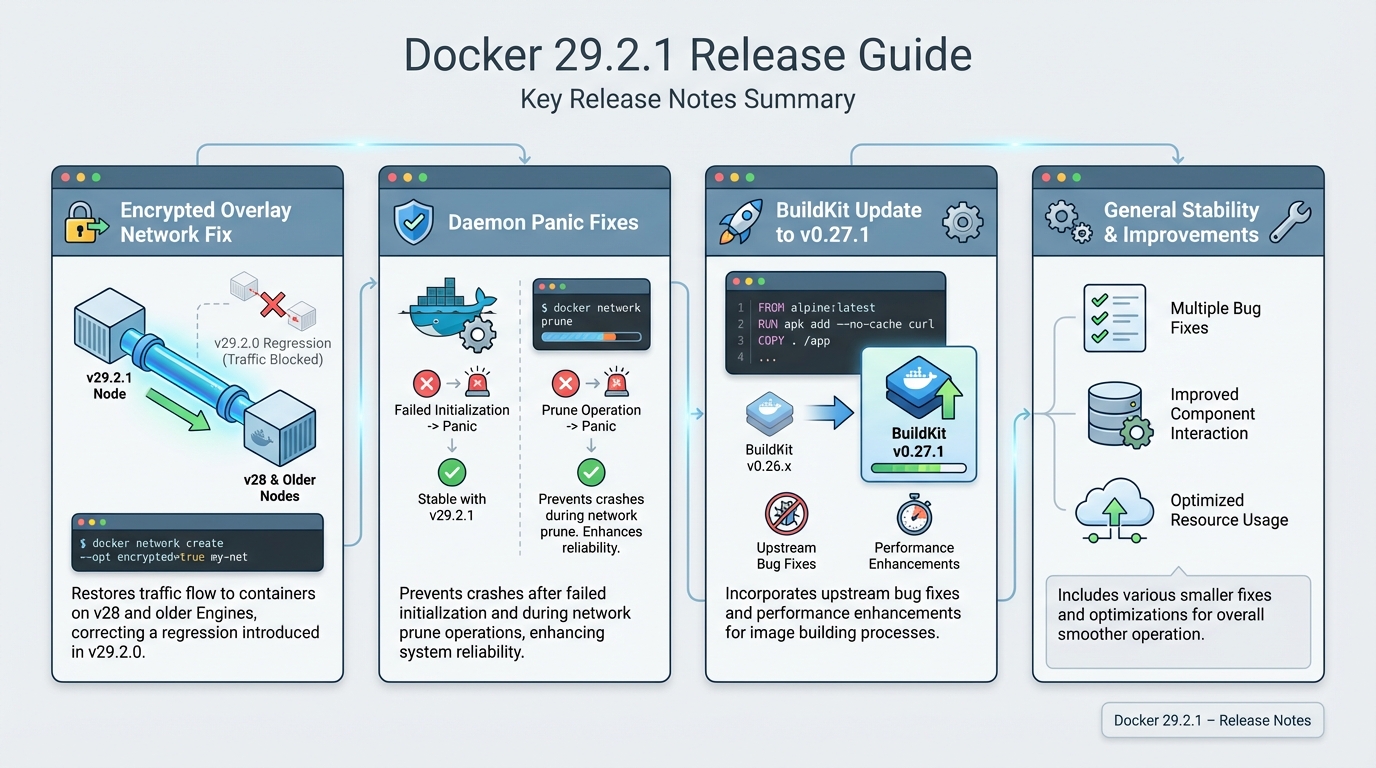
I treat this release as an availability and segmentation risk fix. If you run encrypted overlay networks, 29.2.0 can break east-west traffic in a way that looks like a security incident and burns hours.
Security impact and attack surface changes
The advisory does not specify any CVE IDs for Docker 29.2.1. That does not make this low risk. A daemon panic gives an attacker a denial-of-service primitive if they can trigger the code path, and a broken encrypted overlay can push teams into unsafe “quick fixes” like dropping encryption or punching holes in firewall rules.
- No CVEs called out in the release notes: Treat this as “no public CVE mapping,” not “no security impact.” Verify against Docker security announcements and your SBOM feed.
- BuildKit bumped to v0.27.1 (supply chain surface): Any build system update changes your trust boundary. Pin and test your build pipeline, especially if you use buildx, remote builders, or cache imports.
If you do not upgrade and you hit the overlay regression, teams often disable encryption to restore traffic. That turns a reliability bug into a compliance failure.
Security-relevant fixes (treat as urgent)
This bit me once in a different stack. A “network regression” caused a flood of alerts that looked like lateral movement, then someone suggested “just run it unencrypted for tonight.” Do not do that.
- Encrypted overlay networking regression fixed: Docker fixes encrypted overlay networks not passing traffic to containers on v28 and older Engines. The release notes list affected versions as v29.2.0 through v29.0.0, v28.2.2, v25.0.14, and v25.0.13. If you run mixed fleets, you sit in the blast radius.
- Daemon panic fixes (DoS risk): Docker fixes a panic after failed daemon initialization and a potential panic on docker network prune. A crash loop can take a node out of service and strand workloads.
- Concurrent operations race fixed: Docker fixes docker system df failing when it runs concurrently with docker system prune. This sounds boring until a cleanup job fails mid-incident and you lose visibility.
The encrypted overlay regression, in detail
This is the fix that justifies the patch. Here is what happened.
Docker 29.0.0 through 29.2.0 introduced a regression in how encrypted overlay networks handle IPsec SPIs. When nodes running v29 tried to communicate with nodes running v28 or older, the encrypted tunnel failed silently. Traffic between containers on different hosts just stopped. No error messages, no crash — just dropped packets.
The fix (moby/moby#51951) corrects the SPI negotiation so mixed-version fleets can talk again. But here is the catch: if you already have a mixed fleet running v29.2.0 alongside v28.x nodes, the broken state may persist until both sides restart their Docker daemons after the upgrade. Upgrading the v29 side alone is not always enough.
Check your fleet:
# Find all encrypted overlays
docker network ls --filter driver=overlay --format '{{.Name}}' | while read net; do
encrypted=$(docker network inspect "$net" --format '{{index .Options "encrypted"}}')
[ "$encrypted" = "true" ] && echo "ENCRYPTED: $net"
done
# Check Engine versions across Swarm nodes
docker node ls --format '{{.Hostname}}: {{.EngineVersion}}'If you see mixed versions (any node below 29.2.1) on an encrypted overlay, patch and restart both sides.
What BuildKit v0.27.1 actually changes
The Docker release notes just say “Update BuildKit to v0.27.1” and leave you to figure out the rest. Here is what matters.
BuildKit v0.27.1 is a patch release that fixes cache export reliability and a race condition in concurrent builds sharing cache mounts. If you run docker buildx bake with shared cache or use –cache-to / –cache-from in CI, this patch prevents intermittent cache corruption that shows up as “layer already exists” errors or builds that inexplicably re-download base images.
- Cache export stability: Fixes a race where concurrent builds writing to the same cache destination could corrupt the manifest. This is the one that bites CI pipelines hardest.
- Build context handling: Minor improvements to how build contexts are transferred, reducing memory spikes on large multi-stage builds.
If you pin BuildKit separately (e.g., via docker buildx create –driver-opt image=moby/buildkit:v0.27.0), you need to update that pin too. The Docker Engine bump alone does not change your remote builders.
Breaking changes
The official notes do not list breaking changes for 29.2.1. I still assume you can break something if you rely on undocumented behavior.
So. Run a canary first.
Everything else in this patch
Docker also fixes duplicate container exit event handling to avoid repeated cleanup. You probably only notice this when your logs fill with weird lifecycle noise and your on-call starts guessing.
- Container lifecycle cleanup correctness: Fixes duplicate exit handling to reduce repeated cleanup work and state churn. Specifically, moby/moby#51925 prevents the daemon from processing the same container exit event twice, which could cause log noise and incorrect container state in docker ps.
- Concurrent df/prune race: moby/moby#51979 adds proper locking so docker system df no longer panics when a prune runs simultaneously. If you run monitoring that calls df on a cron while a nightly prune cleans up, this is your fix.
Who should patch before your next standup
Patch today if you run encrypted overlays. Patch today if you run automation that hits prune.
- Immediate: Any production host using encrypted overlay networks, especially mixed Engine versions. Also patch if you run scheduled docker network prune or have seen daemon crashes on startup.
- Within 72 hours: CI builders that depend on BuildKit behavior, caching, or remote builders. The BuildKit bump changes your build surface area.
- Next maintenance window: Single-node dev boxes that do not use overlays and do not run automated prune jobs. You can be less paranoid here.
Upgrade and verification (minimum compliance checklist)
Do not “just yum update” on a fleet. Prove impact, patch a canary, then roll.
# 1. Check current version
docker version --format '{{.Server.Version}}'
# 2. Backup running container list
docker ps --format '{{.Names}}: {{.Image}}' > /tmp/docker-containers-pre-upgrade.txt
# 3. Upgrade (Debian/Ubuntu)
sudo apt-get update
sudo apt-get install docker-ce=5:29.2.1-1~ubuntu.24.04~noble docker-ce-cli=5:29.2.1-1~ubuntu.24.04~noble
# 4. Restart daemon
sudo systemctl restart docker
# 5. Verify version
docker version
# 6. Check all containers restarted
docker ps --format '{{.Names}}: {{.Status}}'
# 7. Test encrypted overlay connectivity
docker exec ping -c 3
# 8. Watch for panics
journalctl -u docker.service --since "5 min ago" | grep -i panic For RHEL/CentOS, replace the apt commands with yum install docker-ce-29.2.1 and adjust the version string for your repo. For Docker Desktop, check the Desktop release notes separately — Desktop ships its own Engine version on a different cadence.
Docker 29 release timeline
Context matters. Here is where 29.2.1 sits in the Docker 29 lifecycle:
- 29.0.0 (Oct 2025) — Major release. New NRI (Node Resource Interface) support, gRPC API improvements, containerd 2.0 integration. This is where the overlay regression was introduced.
- 29.1.0 (Dec 2025) — Minor release with improved container lifecycle management and image store fixes.
- 29.2.0 (Jan 2026) — Added experimental NRI hooks and further gRPC support. Still carried the overlay bug.
- 29.2.1 (Feb 2026) — This patch. Fixes the overlay regression, daemon panics, and BuildKit bump. This is the version you should be running.
Docker 28.x is still supported. If you cannot move to 29, note that 28.2.2 also had the encrypted overlay issue. The fix was backported to the 28 line — check the Moby releases page for the patched 28.x version.
Until we see a PoC, the real risk is operational: a crash loop or a “temporary” removal of network encryption under pressure.
Known issues
The official release notes do not list known issues for 29.2.1. I do not trust “none” as a guarantee. Anyway.
References
- Moby/Docker Engine v29.2.1: github.com/moby/moby/releases/tag/docker-v29.2.1
- Overlay fix PR: moby/moby#51951
- BuildKit v0.27.1: github.com/moby/buildkit/releases/tag/v0.27.1
Related Reading
🛠️ Try These Free Tools
Paste your Kubernetes YAML to detect deprecated APIs before upgrading.
Paste a Dockerfile for instant security and best-practice analysis.
Plan your upgrade path with breaking change warnings and step-by-step guidance.
Track These Releases