Node.js 24.14.0 release notes: what the community cares about
Reddit’s already nitpicking the proxy API, and the embedders are quietly cheering.
The consensus seems to be that Node.js 24.14.0 “Krypton” (LTS, 2026-02-24) is a safe-ish minor upgrade for most Node 24 fleets, but only after you test the SQLite default change and check your binary size if you ship slim containers.
Community take: what people are actually talking about
I’ve watched this pattern play out every LTS minor. Somebody posts “anything scary?” and three SREs reply with “we canaried it, looks fine,” then one person drops a weird edge case and everyone piles on.
That’s basically 24.14.0 so far. The loudest threads are about debugging async promise chains, the new global proxy helper, and “wait, why did my Node binary get bigger?”
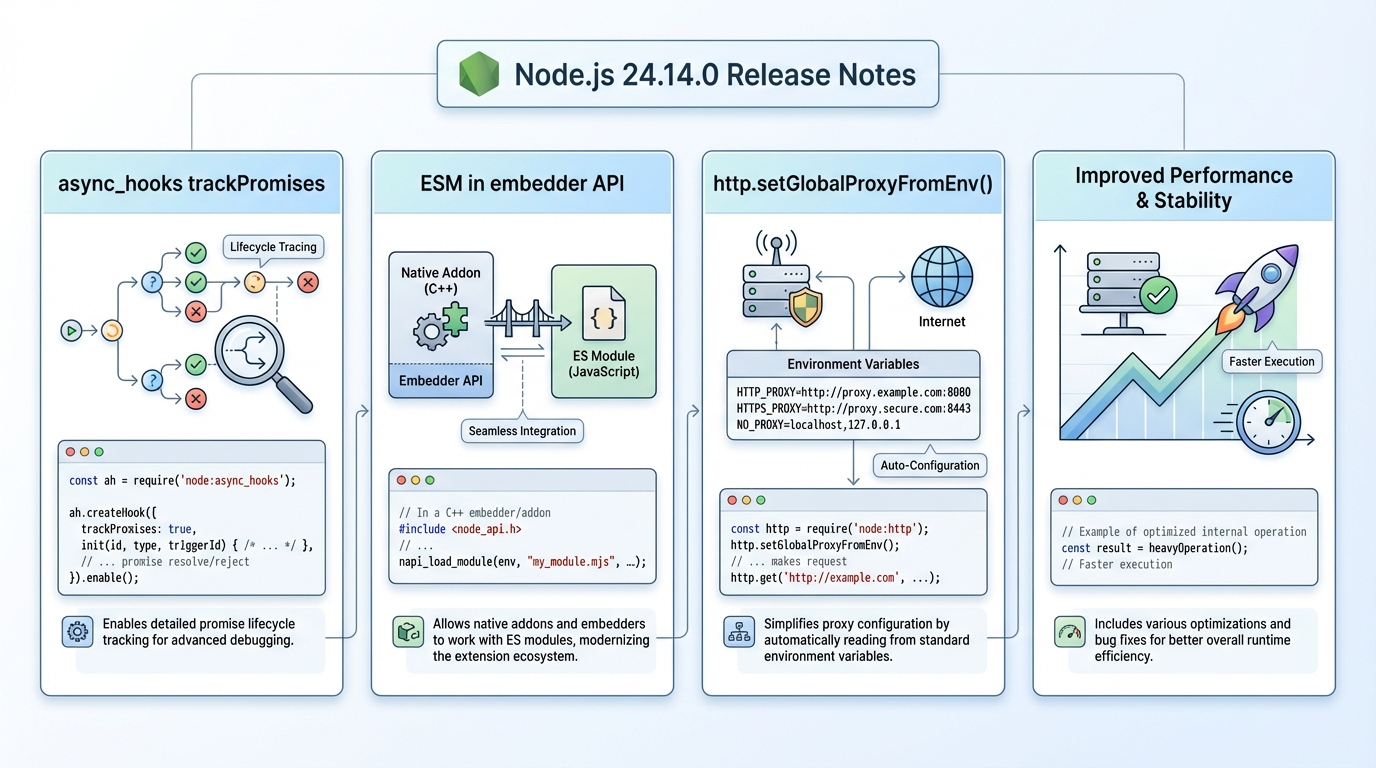
- Async debugging got real attention: Folks who live in async stack traces keep pointing at async_hooks promise lifecycle tracking as the headline. As one SRE put it, “If you’ve ever stared at a hung promise chain at 2 a.m., you’ll try anything.”
- Proxy config is a small feature with big enterprise energy: On Slack-type channels, the chatter is basically “finally, one blessed place to read HTTP_PROXY/HTTPS_PROXY/NO_PROXY.” Some teams report it “just works,” others warn that global proxy settings can surprise libraries if you set it too early in process startup.
- Embedders perked up: The embedder API getting initial ES module support is a niche change, but the people who build runtimes and host Node inside other apps care a lot. The vibe is “this is Node admitting ESM is the default future, even for hosts.”
- Binary size concerns are real: The LIEF dependency shows up in the “why did my image grow?” conversations. If you run tight serverless budgets, you’ll notice. If you ship big base images anyway, you probably won’t.
So. Do you upgrade today?
Most teams are upgrading, but they are doing it with canaries and a rollback plan. Some folks skip canaries for minor releases. I don’t, but I get it.
Official changelog highlights (v24.14.0)
Here’s what upstream actually shipped in v24.14.0. I’m keeping it to the parts I’ve seen people ask about in issues and chat, not every single internal refactor.
- async_hooks: Added trackPromises option to createHook() for promise lifecycle tracking.
- src (embedder API): Added initial support for ES modules in the embedder API.
- http: Added http.setGlobalProxyFromEnv() to configure proxy behavior from environment variables.
- fs: Added an ignore option to fs.watch so you can filter event noise (think tmp files and node_modules churn).
- sqlite: Added prepare options arguments, and enabled defensive mode by default (this is the one I’d actually regression-test).
- node:stream/consumers: Added a bytes() consumer that returns byte data efficiently (useful when you’re tired of accidental string conversions).
- test_runner: Added an env option to run() for passing environment into tests.
- util: Added convertProcessSignalToExitCode utility.
- build: Added support for Visual Studio 2026.
- deps/tools: Added LIEF and wired it into license builder tooling.
- deps: Updated npm to 11.9.0 and undici to 7.21.0.
My synthesis: who should care, and what’s the risk
This bit me once: a “harmless” default change in a DB binding turned into a latency spike that only showed up under real traffic.
That’s why I’m more interested in the SQLite defensive mode default than any shiny new API. If you run high-throughput SQLite usage in-process, test it under your real concurrency, not a toy benchmark.
- If you debug async weirdness weekly: You probably want 24.14.0 for trackPromises. It won’t fix your architecture, but it can make the failure visible.
- If you run behind corporate proxies: http.setGlobalProxyFromEnv() reduces setup code, but global settings can leak into places you didn’t expect. Try it in staging first.
- If you ship tiny containers: watch your artifact sizes after the LIEF change. The exact delta depends on platform and build details.
- If you maintain native addons or embed Node: the embedder API ESM work is a clear signal. Still, “initial support” usually means “expect rough edges.”
I don’t trust “known issues: none” from any project. Treat it as “none listed,” then go look at the issue tracker yourself.
Upgrade plan (what most teams are doing)
Take a canary.
In most cases, a 5% canary on a single service tells you more than an hour of reading release notes, especially for changes like proxy behavior and SQLite defaults.
- Step 1, pick one service: Choose the one with the ugliest async behavior or the strictest proxy environment. That’s where you’ll learn fastest.
- Step 2, upgrade Node: Use nvm (nvm install 24.14.0 && nvm use 24.14.0) or your standard Docker base image bump.
- Step 3, run your “real” smoke tests: Login flows, background jobs, stream-heavy endpoints, whatever actually pages you.
- Step 4, watch two graphs: p95 latency and error rate. If you do not have those, do not do a fleet-wide upgrade.
- Step 5, keep rollback boring: Pin the previous Node 24.x version in CI and images so you can revert in one commit.
Quick examples (correct shapes, not a full tutorial)
These are the “paste into a scratch file” examples I’ve seen people share in Discord when they want to sanity-check a new API.
I haven’t tested every snippet on every platform, so treat them as starting points and cross-check the docs.
- Promise lifecycle tracking: Use async_hooks.createHook({ init, destroy, promiseResolve, …, trackPromises: true }) and log promise IDs while you reproduce the bug.
- Global proxy from env: Call http.setGlobalProxyFromEnv() once during startup, then make a simple HTTPS request and confirm it respects your HTTPS_PROXY and NO_PROXY rules.
- fs.watch ignore: Add ignore patterns like node_modules and *.tmp, then run your build and see if your watcher stops screaming.
- Consume bytes from a stream: Import from node:stream/consumers and read a response body as bytes when you need a Uint8Array, not a string.
Known issues (reality check)
No upstream release note can promise you a quiet upgrade.
As of the release notes publication, upstream does not list specific known issues for v24.14.0. That does not mean you won’t hit one. Anyway.
- Artifact size changes: LIEF can increase binary size depending on platform and build choices. Measure your Node binary and container image before you roll it everywhere.
- SQLite behavior: Defensive mode by default can change performance characteristics. If SQLite sits on your hot path, benchmark it under load.
Read the official notes, skim the linked PRs, then trust your canary more than my vibes. There’s probably a better way to test this, but…
🛠️ Try These Free Tools
Paste a Dockerfile for instant security and best-practice analysis.
Paste your dependency file to check for end-of-life packages.
Plan your upgrade path with breaking change warnings and step-by-step guidance.
Track These Releases