ExternalServiceAccountTokenSigner goes GA (authn plumbing becomes an SLO issue)
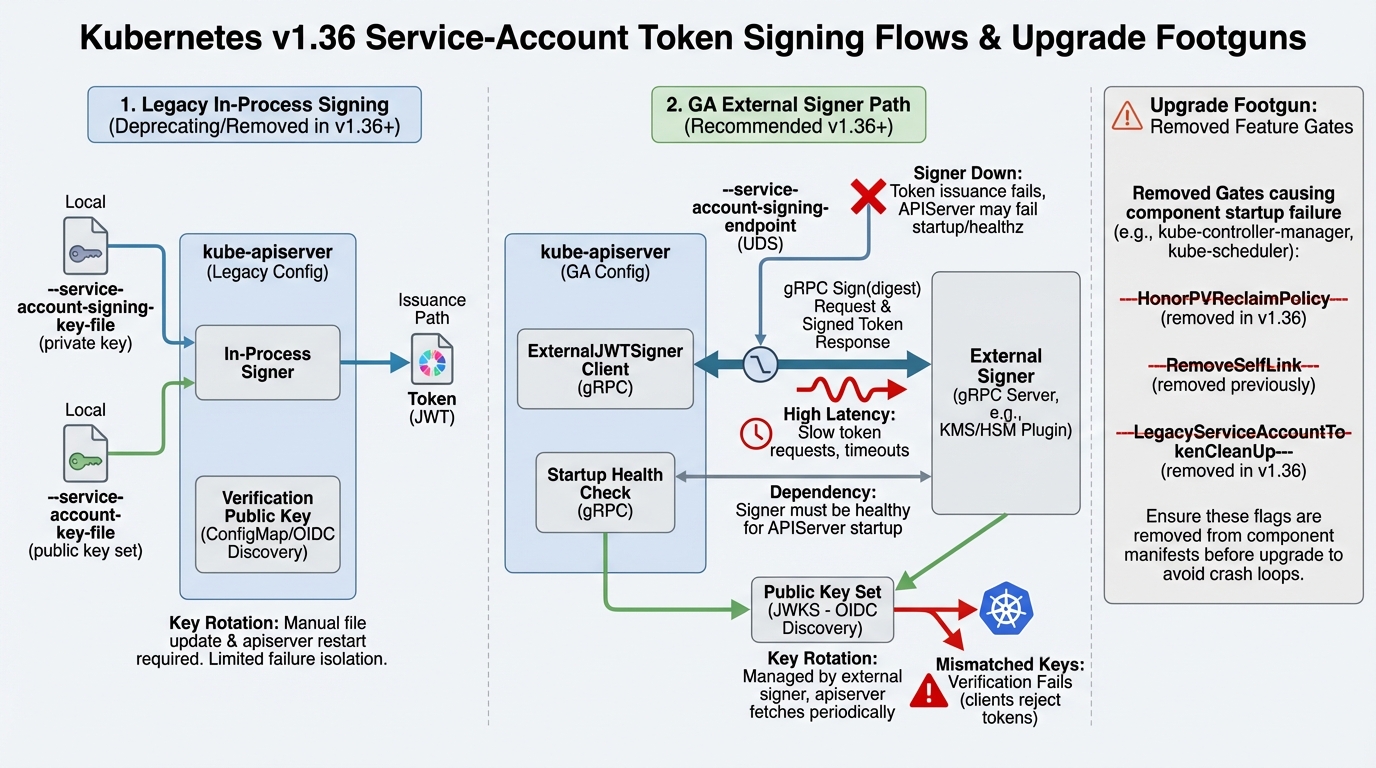
PR #136118 promotes ExternalServiceAccountTokenSigner to GA and locks the gate on. The external signer path (configured via –service-account-signing-endpoint) stops being an experiment and starts being part of the supported surface area. The kube-apiserver can now delegate signing and key management to an external process (UDS + gRPC).
So what? Teams running HSM / cloud-KMS-backed signing finally get an upstream-blessed path instead of distro-specific patches. The flip side: signer availability and latency become control-plane critical. A sick signer is no longer “some beta integration acting weird”; it’s now a first-class way to take your API server down.
Gotcha: the docs are explicit that file-based signing flags and the endpoint are mutually exclusive. Mixed configs (common in templated kubeadm manifests and vendor overlays) will bite you during rollout.
HonorPVReclaimPolicy feature gate removed (your binaries won’t start if you cling to it)
PR #135335 removes the HonorPVReclaimPolicy feature gate in 1.36. This is not a “behavior changed a bit” situation. A removed gate means the component flag parsing can hard-fail. You don’t get to limp along with a warning.
So what? Your upgrade risk isn’t in runtime behavior; it’s in process start. CI that only validates Kubernetes objects but never boots a real control plane is about to look very optimistic.
Gotcha: managed services sometimes keep a shadow config for control-plane flags. You can remove the flag in your repo and still have the provider injecting it. Audit both.
RealFIFO / InOrderInformers promoted to GA (client-go ordering stops being optional)
PR #136601 graduates InOrderInformers (RealFIFO) to GA. The PR discussion is blunt: they want to lock it on and “start the clock” to delete older, less-correct paths.
So what? If you maintain controllers/operators, you need to validate assumptions about informer delivery ordering and any subtle race masking you were getting from older queue behavior. Most code will be fine. The weird stuff—homegrown caches, event coalescing, brittle tests that implicitly relied on reorder—will start flaking.
Gotcha: watch your test harnesses. The PR thread calls out compatibility mode concerns for unit tests that toggle gates. Translation: your downstream “it still passes on 1.35” suite can lie.
Kubernetes isn’t chasing shiny features here; it’s paying down debt in the most Kubernetes way possible: by turning “optional” behavior into the default, then deleting escape hatches. External JWT signing going GA tracks the reality of modern security posture: key custody is leaving the node filesystem. Meanwhile, feature-gate removal is the project forcing operators to stop running museums.
The subtext: upstream is drawing harder boundaries around what’s supported. If you’re a distro, you get a cleaner contract. If you’re an SRE, you get fewer toggles to save you when something misbehaves. Pick your poison.
Target for preview testing is v1.36.0-beta.0 (planned 2026-03-11). Don’t wait for 1.36.0 if you care about avoiding ugly surprises.
Test the beta (cluster bring-up)
git clone https://github.com/kubernetes/kubernetes cd kubernetes # Build or use your preferred tooling; the key is: boot a real control plane. # If you use kind, you’ll need an image that matches 1.36 beta once published.
External JWT signer (kube-apiserver flags)
# External signer enabled via Unix domain socket (UDS) # Example flag (actual socket path depends on your deployment): --service-account-signing-endpoint=/var/run/kubernetes/external-jwt-signer.sock # Ensure you are NOT also setting: # --service-account-key-file # --service-account-signing-key-file
Red Flags to watch for in logs
- Unknown feature gate / unrecognized feature gate (component startup failure). Hunt for removed flags like HonorPVReclaimPolicy.
- External signer health / connection failures during kube-apiserver startup or token issuance paths (UDS connect errors, gRPC deadline exceeded).
- Controller/operator flake: cache sync weirdness, reflector warnings, or tests that start failing only under load—classic symptom of latent ordering assumptions.
🛠️ Try These Free Tools
Paste your Kubernetes YAML to detect deprecated APIs before upgrading.
Plan your upgrade path with breaking change warnings and step-by-step guidance.
Paste your Terraform lock file to check provider versions.
Track These Releases