Kubernetes 1.36 Beta: the community’s take on “fewer knobs”
Reddit’s already arguing about this one. Most teams aren’t hyped, they’re nervous about upgrades that fail before the first pod even schedules.
Community take first: what people are worried about
I’ve watched this exact movie in #kubernetes on Slack. Somebody says “it’s just a beta,” then their control plane refuses to come up because one flag or one dependency moved from optional to required.
Two threads keep popping up in side chats and PR comments. Folks like the direction, but they hate surprises.
- “GA means you own the SLO now” (PR #136118): Teams that wanted HSM or cloud-KMS backed signing feel seen. Teams that run a fragile sidecar signer feel exposed.
- “Stop shipping museums” (PR #135335): People generally support deleting dead gates, but nobody wants to discover it during a 2am maintenance window.
- “Controller authors, please run your tests twice” (PR #136601): Maintainers keep hinting that the old paths won’t live forever, so operator code that relied on old informer quirks should get a reality check.
Some folks skip canaries for betas. I don’t, but I get it.
Official highlights (what actually changed in the PRs)
PR #136118: ExternalServiceAccountTokenSigner goes GA
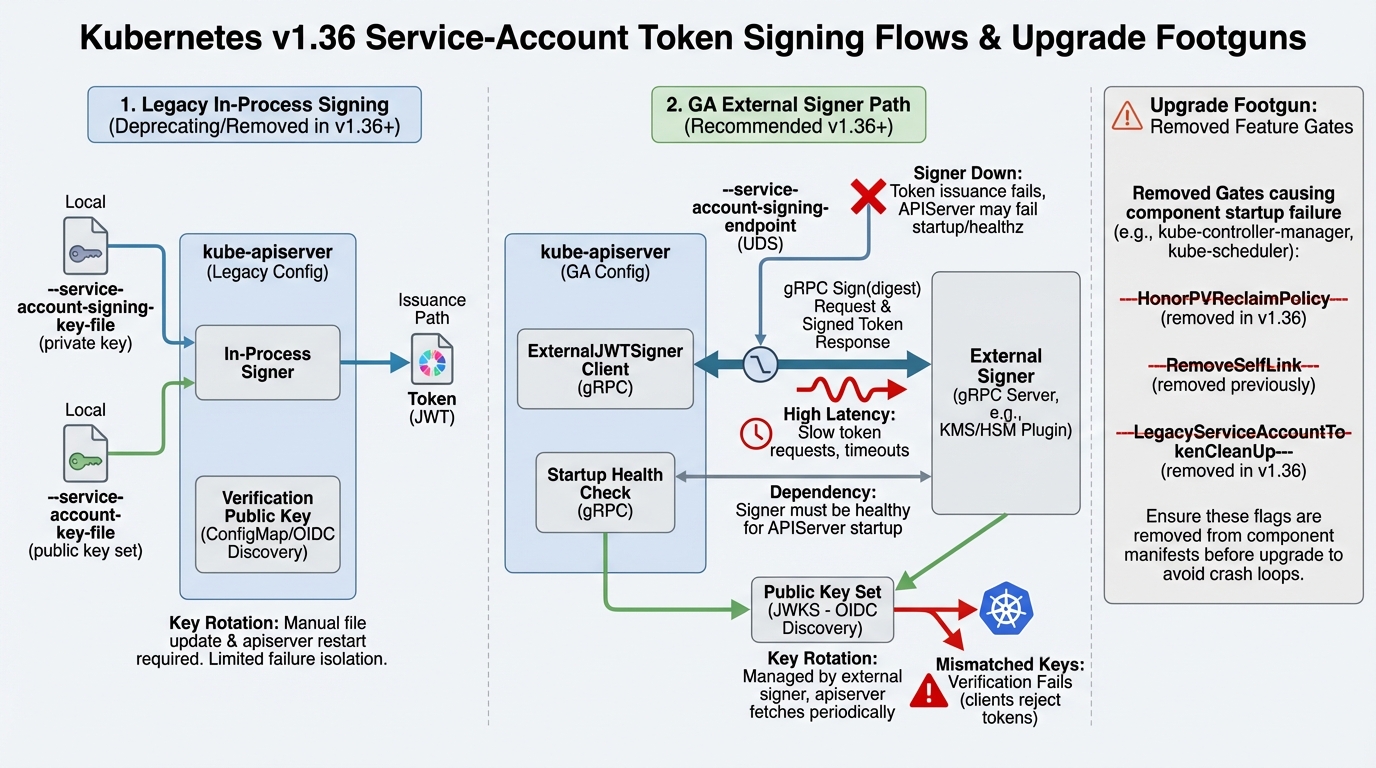
This change makes the external service account token signer a supported, stable path. You wire it up with –service-account-signing-endpoint, and kube-apiserver talks to a signer over UDS and gRPC.
Good. Also scary.
I’ve seen teams treat token signing like “that file on disk we never touch.” Once you move signing to an external process, that process becomes part of your control plane’s day-to-day health story.
- Why people want it: It gives you an upstream path for HSM and KMS key custody instead of distro patches and homemade controllers.
- What bites during rollout: The docs say file-based signing flags and the endpoint are mutually exclusive. If your kubeadm templates set both, expect a bad time.
If you configure an external signer, treat it like a control-plane dependency. Monitor its latency, not just “is the pod running.”
PR #135335: HonorPVReclaimPolicy feature gate removed
This one looks boring until it isn’t. The PR removes the HonorPVReclaimPolicy feature gate, which used to be locked on in recent releases.
So.
Do not assume “removed gate” equals “my cluster won’t boot.” Upstream PR text doesn’t prove that. What it does mean is simpler: you cannot toggle it anymore, and any automation that still tries to set it needs attention.
- What to do this week: Grep your kube-apiserver, controller-manager, scheduler, and kubelet flag sources for HonorPVReclaimPolicy. Check Helm values, kubeadm patches, and systemd drop-ins.
- If you run managed Kubernetes: Ask your provider how they manage control-plane flags. If they do not show you, assume you still need to test behavior, not flags.
PR #136601: RealFIFO and InOrderInformers go GA
Controller people noticed this immediately. InOrderInformers (RealFIFO) going GA signals that ordering stops being a “maybe” and starts being the expected path.
Most controllers will shrug.
The ones that won’t are the weird ones. The hand-rolled caches, the tests that pass only because timing jitter hides a race, the “it only flakes on Tuesdays” suites.
- Where you’ll feel it: Operator/controller integration tests under load, especially if you coalesce events or assume a certain delivery order.
- How to catch it early: Run your controller tests on 1.36-beta with load, then rerun them. If the second run fails differently, you probably have an ordering or timing dependency.
My synthesis: this release pushes contracts, not features
The consensus seems to be that upstream is tightening the supported surface area. You get fewer toggles, and you get cleaner expectations.
That’s healthy. It’s also unforgiving.
Strong opinion: if you cannot boot a real control plane in CI, you should not call your upgrade process “tested.” YAML validation doesn’t catch “process won’t start.” It catches nothing about dependencies like external signers.
What most teams are doing: test the beta like it’s a bring-up drill
The beta is scheduled for 2026-03-11. If you’re reading this during a quiet week, that’s your window to break things on purpose and fix your runbooks.
Bring up a real control plane
Boot something real. Kind, kubeadm, whatever you trust.
CI that only applies manifests lies to you. A control plane either starts clean, or it doesn’t.
External signer config sanity check
Set the endpoint, and make sure you do not also set file-based signing flags in the same apiserver config.
- Example: –service-account-signing-endpoint=/var/run/kubernetes/external-jwt-signer.sock
- Do not combine with: –service-account-key-file, –service-account-signing-key-file
Red flags to watch in logs
- Unknown feature gate / unrecognized feature gate: Treat it as “stop the rollout.” Find the template that still sets it.
- Signer connection failures: UDS permission errors, connect failures, gRPC deadline exceeded. If tokens fail to mint, you will feel it fast.
- Controller weirdness: cache sync stalls, reflector warnings, tests that only fail under load. That’s usually a real bug, not “CI being flaky.”
Other stuff in this release: dependency bumps, some image updates, the usual. There’s probably a better way to test informer-ordering edge cases, but…
🔍 Free tool: K8s YAML Security Linter — paste any Kubernetes manifest and instantly catch security misconfigurations: missing resource limits, privileged containers, host network access, and more.
🛠️ Try These Free Tools
Paste your Kubernetes YAML to detect deprecated APIs before upgrading.
Paste your dependency file to check for end-of-life packages.
Plan your upgrade path with breaking change warnings and step-by-step guidance.