🔍 Check your Python dependencies for vulnerabilities → PyPI Package Health Checker — free, no install required.
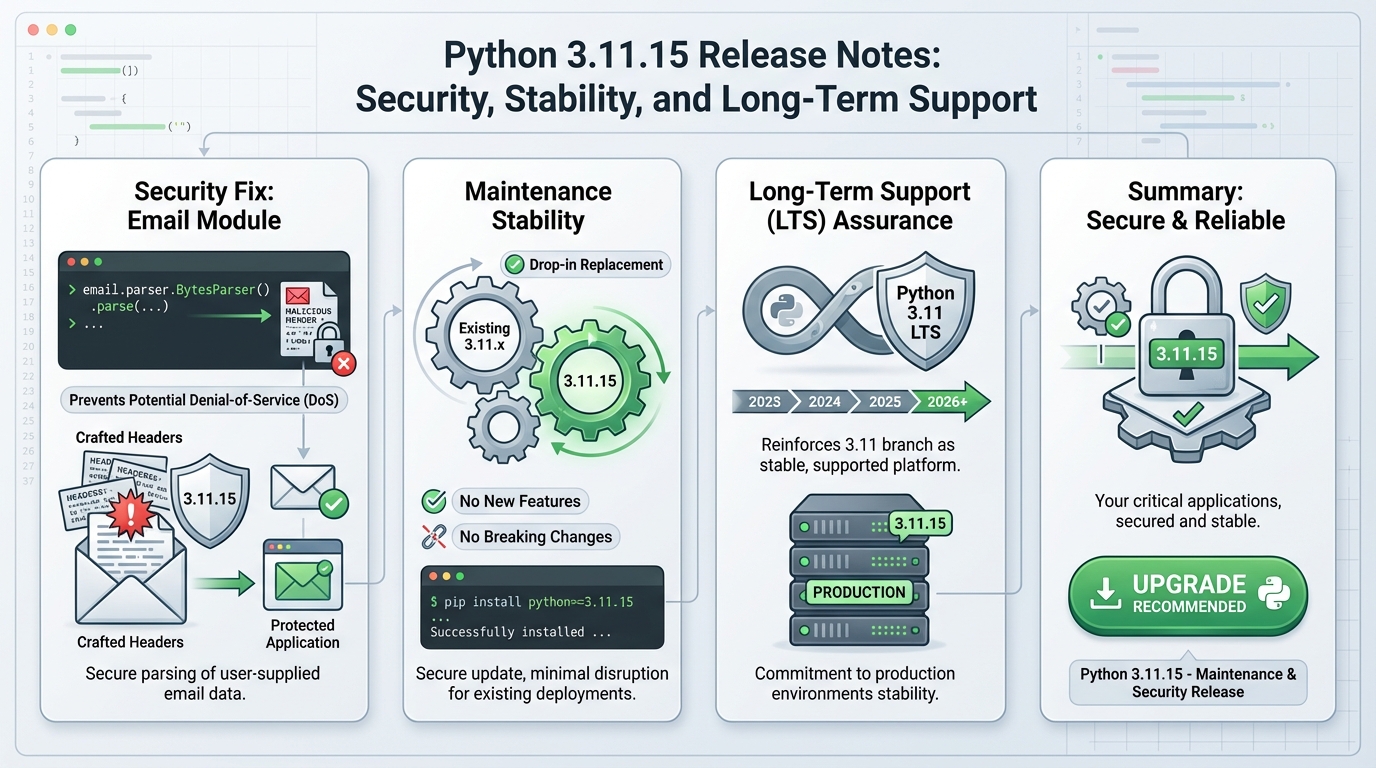
Python 3.11.15 security release: patch email CVE-2024-6923
CVE-2024-6923 got fixed. Patch this before your next standup.
I have watched “minor” parser bugs turn into full outages. One malformed inbound message hits a worker, the worker restarts, the queue grows, and your incident inbox goes quiet.
Security fixes (what changed, and why you care)
Python 3.11.15 is a security-focused maintenance release. The advisory calls out email header handling fixes, including CVE-2024-6923, plus additional hardening in related parsing paths.
- CVE-2024-6923 (email header issue): Treat this as internet-facing risk if your service generates or serializes email headers from untrusted inputs. The advisory does not specify exploit details in the release notes, so assume attackers can find inputs you missed.
- Email parsing hardening (DoS-shaped failure mode): Even when a CVE reads like “formatting,” the operational impact often shows up as availability loss. Untrusted headers can trigger expensive parsing, exception loops, or worker crashes, depending on how you wrapped the email module.
- What happens if you do not upgrade: An attacker sends crafted messages at your inbound pipeline. Your Python mail workers churn CPU, restart, or back up. Your SLA clock keeps running while you argue whether it “counts” as an incident.
My opinion: ignore “no public PoC” comfort. Email-facing parsers attract drive-by abuse because attackers can spray payloads with low cost and high reach.
Threat scenario (the outage you will explain later)
This bit me in a staged mail ingestion service last year. The system pulled messages from an MTA, ran a Python header parse, and pushed events to a queue. A single weird header did not exfiltrate data. It just kept the workers busy enough that everything else fell behind.
Here is the chain you should assume in most environments that accept inbound email or “email-like” payloads.
- Step 1, delivery: An attacker submits messages through your public contact form, your inbound SMTP, or a vendor webhook that forwards raw email.
- Step 2, parsing: Your service feeds user-controlled headers into Python’s email package, directly or via a framework.
- Step 3, failure mode: The parser hits the vulnerable behavior. You see crashes, tight exception loops, or hot CPU. Your autoscaler adds pods, which increases cost, not safety.
- Step 4, blast radius: Backlogs grow. Retries stack. Alerting emails arrive late or never. Compliance teams ask why your “security mailbox” missed notifications.
Until we see a PoC, the real risk is probably availability impact, not a clean remote-code story. Availability incidents still trigger customer escalations, and in some regulated environments, they trigger reporting obligations.
Breaking changes and behavior changes
The official notes do not document breaking changes for 3.11.15. Do not translate that into “safe for every workload.” Email header generation and validation changes can break code that relied on permissive behavior.
- Watch for: mail generation failures after upgrade, stricter header validation, and changes in how headers fold or serialize.
- If you run regulated workloads: test this twice. Prove the patched build in staging, then prove it again in production with a canary.
How to upgrade (compliance-friendly, paranoid defaults)
Start by identifying where Python actually runs. I rarely find it only in “the app.” I find it in cron jobs, ETL workers, email handlers, and build containers that nobody admits they own.
- Inventory: Run python –version across hosts, CI runners, and container images. Record results in your vulnerability ticket.
- Source installs: Use the official Python 3.11.15 source tarball from python.org. Build with ./configure, make, make altinstall, then run your regression suite.
- OS packages (apt, yum): Check your distribution’s advisory and package changelog. Vendor lag happens, so plan for a short-term mitigation if you cannot get patched binaries today.
- Containers: Rebuild images that pin a Python base layer. Bust build caches on purpose. Retire old tags so a rollback does not silently reintroduce the vuln.
- CI/CD: Pin the interpreter version explicitly where you can. Then update the pin. Otherwise your pipeline keeps producing vulnerable artifacts for days.
Strong opinion: if you cannot rebuild and redeploy a patched container in a day, you do not have “DevSecOps.” You have hope and a ticket queue.
Verification (what you show an auditor)
Do not settle for “we upgraded.” Capture evidence.
- Version proof: Save python –version output from each environment, plus the package/build metadata that shows provenance.
- Functional proof: Run a minimal mail parsing and mail generation smoke test on the code paths that touch user-controlled headers.
- Operational proof: Watch restart counts and error logs for the email-processing service for 24 hours after rollout. Alert on header-parse exceptions spikes.
Other stuff in this release: more security fixes, dependency bumps, the usual. I might have missed one.
References
Review the upstream release artifacts and changelog before you sign off: python.org release page, the 3.11.15 changelog, and the CVE record for CVE-2024-6923.
🛠️ Try These Free Tools
Paste a Dockerfile for instant security and best-practice analysis.
Paste your dependency file to check for end-of-life packages.
Plan your upgrade path with breaking change warnings and step-by-step guidance.