Python 3.15.0a7 release notes: the quiet alpha with sharp edges
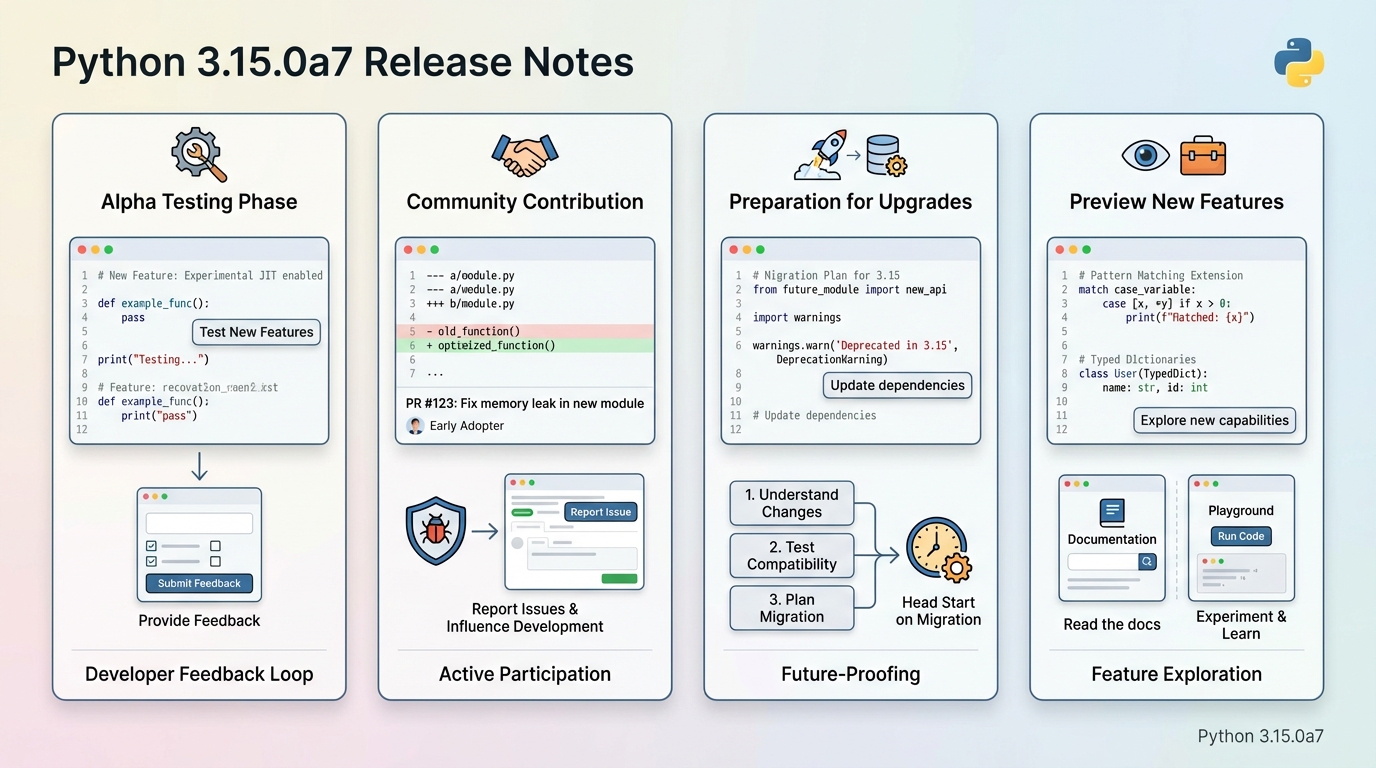
Three months into the Python 3.15 cycle, alpha 7 showed up with a familiar message: test it, break it, tell us where it hurts.
And yes, this is still alpha territory. You do not put it on production boxes unless you enjoy explaining outages that start with “we only changed the interpreter.”
Where this alpha sits in the Python 3.15 story
I’ve watched teams ignore alphas for months, then panic when beta lands and their CI starts screaming. The alphas exist to move that pain earlier, while changes still feel negotiable and bug reports still influence what ships.
Python 3.15.0a7 came out on March 10, 2026, and it reads like one of those releases that looks “small” until it trips a build farm at 2 a.m. If past releases are any guide, the bugs you catch here save you two rounds of emergency pinning later.
What actually changed in 3.15.0a7 (selected highlights)
The thing nobody mentions is that “alpha” does not mean “nothing happening.” It often means the changes hide in platform corners, C extensions, and behavior fixes that only show up when your tests run hot.
- Windows time handling got a fix: CPython fixed a negative timestamp during DST on Windows. If you run schedulers, log shippers, or anything that compares timestamps across time zones, this belongs on your smoke-test list.
- hashlib/hmac crash-class bugs got attention: The changelog calls out double-free and null pointer dereference fixes in rarer error paths. You probably never hit them. Until you do, under load, in the one service that signs tokens.
- ctypes behavior shifted on Windows: CPython deferred loading psapi.dll until ctypes.util.dllist() uses it. If you ship tooling that pokes at processes or DLL lists, test the import path, not just runtime behavior.
- OpenSSL in installers moved forward: The release notes mention an updated bundled OpenSSL version. If you build wheels, ship embedded Python, or rely on specific TLS behavior, you want this in a controlled test matrix.
- Stdlib and error messages got sharper: ModuleNotFoundError now includes better hints in some cases, and that sounds cosmetic until you realize your support team will copy-paste those hints into tickets for the next year.
Some folks skim commit counts like they predict risk. I don’t. A single change in a loader path can ruin your Friday more reliably than 300 drive-by doc fixes.
Who should bother testing this alpha, and who should back away
Test it if you maintain a library, a build tool, or a deployment pipeline that touches Python at the edges. Skip it if you barely control your dependency graph and your “staging” environment shares a database with production, because you will lie to yourself about safety.
- Library maintainers: Especially if you ship C extensions or wheels. Import failures and ABI mismatches show up early, and you want time to respond before users start opening issues with “Python 3.15 broke everything.”
- DevOps and CI owners: If your pipeline builds images, runs tests, or lints code under multiple Python versions, add 3.15.0a7 as an allowed-fail job now. You want the signal without blocking merges.
- API teams with long-lived services: If you plan to adopt 3.15 quickly after final, you can start mapping deprecations and behavior changes while you still have slack in the schedule.
How I’d test 3.15.0a7 without wrecking my week
Keep it boring. That’s the trick.
Install it in a sandbox, run a narrow set of tests that cover imports, extensions, crypto, and time handling, then file one high-quality bug instead of five vague ones. The team says “test and report,” but history suggests maintainers ignore reports that lack build flags, platform details, or a minimal reproducer.
- Use isolation on purpose: Install in a virtual environment and keep it away from system Python. If you run pyenv, even better. If you run containers, this gets easier and also more honest.
- Run a smoke suite first: Import your top 20 dependencies, run your CLI entry points, compile your package, then run the smallest slice of tests that touches your real runtime paths.
- Then run one “pain test”: If you handle TLS, hammer your handshake code. If you parse archives, hit tarfile paths. If you run on Windows, run timezone and timestamp tests around DST boundaries.
For a dev cluster, yolo it on a throwaway runner. For critical systems, test this twice, on two machines, and do not trust a green run until you’ve reproduced it on the same OS build your customers use.
Known issues: what we can say, and what we cannot
No official “known issues” list shows up on the release page for 3.15.0a7, which is not the same thing as “nothing is wrong.” Alphas collect their known issues in issue trackers, CI dashboards, and maintainer DMs that never become release notes.
If you see “Known issues: none,” treat it as “Known issues: nobody wrote them down yet.”
What comes next, and why alpha reports matter now
Python’s release train tightens as it approaches beta, when behavior changes become harder to justify and regressions get more expensive to fix. This is the window where maintainers can still say, “This breaks our extension build,” and actually influence the outcome.
Other stuff in this release: dependency bumps, build tweaks, platform papercuts, the usual. There’s probably a better way to prioritize alpha testing than my checklist, but it keeps me honest when the calendar gets crowded.
If you’re going to do one thing, do this: run your project under 3.15.0a7 in a clean environment, capture the first failure with full logs, and link it to the upstream release notes when you report it.
Make sure your dependencies are ready with the free PyPI Package Health Checker — check any Python package for latest version, release date, and deprecation status before you upgrade.
🛠️ Try These Free Tools
Paste your dependency file to check for end-of-life packages.
Plan your upgrade path with breaking change warnings and step-by-step guidance.
Compare EKS, GKE, and AKS monthly costs side by side.
Track These Releases