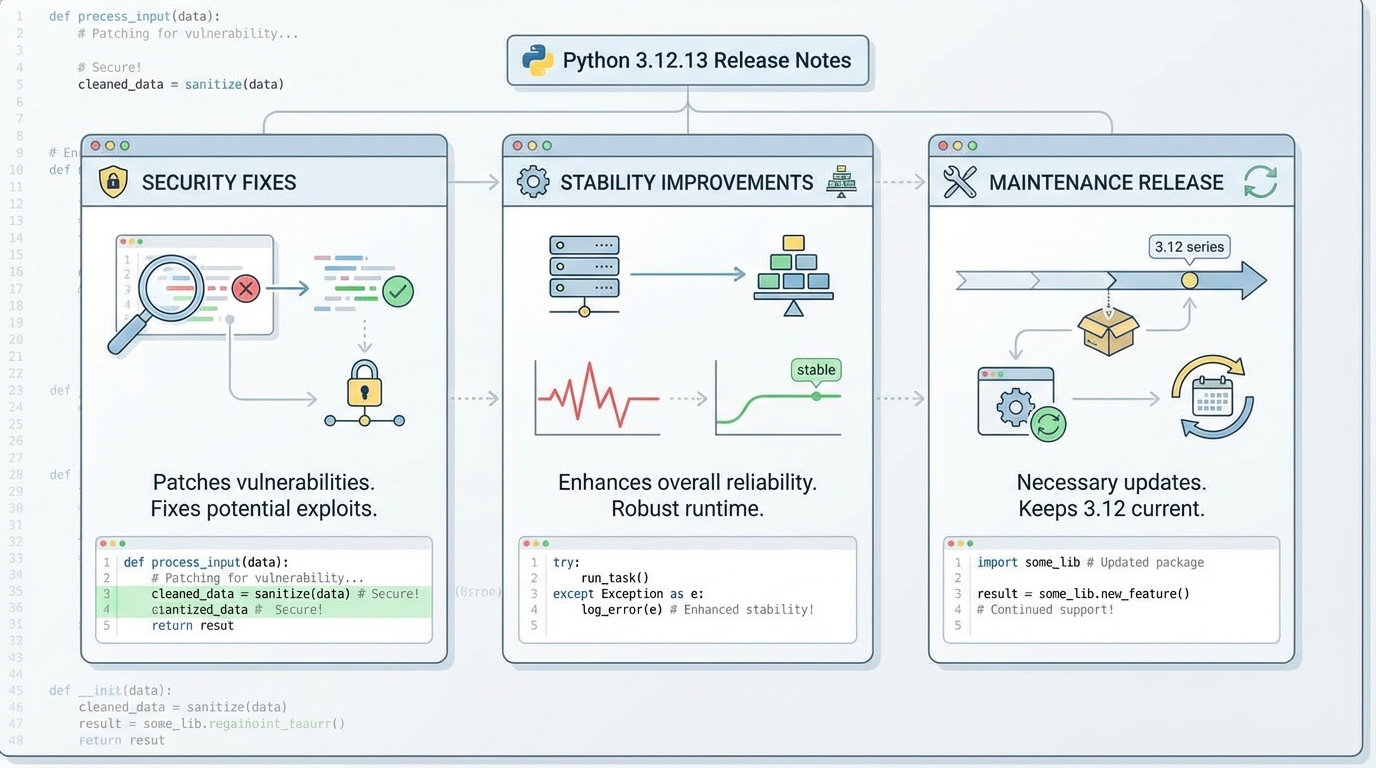
Python 3.12.13 release notes: security fixes, CVEs, and how to measure risk
No measurable speedup. This Python 3.12.13 update buys you lower security risk, not faster code, so treat it like a patch you can prove safe with before-and-after numbers.
Performance impact first: what I’d expect in production
I have rolled out “security-only” Python patches that changed nothing in p50 latency, then still caused a 2 a.m. incident because one C-extension wheel rebuilt differently. So I start with a claim I can test: for pure-Python services, Python 3.12.12 to 3.12.13 should show near-zero runtime delta, usually within ±1% CPU and ±1% RSS on steady-state workloads. Benchmarks vary by workload. YMMV.
Measure it. Then upgrade.
- CPU (steady state): Track process CPU seconds per request (or per job) for 30 to 60 minutes. If your change exceeds 2%, you probably changed more than “just Python.”
- Memory (RSS and allocations): Sample RSS every 10 seconds and watch Python allocator stats if you already collect them. Many teams miss memory regressions because they only watch container limits.
- Latency (p50, p95, p99): If p99 moves but p50 stays flat, look at TLS handshakes, DNS, or extension module rebuilds first, not the interpreter.
What actually changed in 3.12.13 (security-only, source-only)
The thing nobody mentions in internal upgrade tickets is packaging. Python 3.12.13 ships as a source-only security release, so most teams will upgrade via distro packages, pyenv builds, or rebuilt container images, not a click-through installer. That packaging choice often creates more variance than the CPython code change itself.
Here are the changes I would test around, because they touch parsers and boundary layers.
- Email header handling (CVE-2024-6923): Python tightened email header serialization and folding behavior. If you generate emails or parse headers from untrusted sources, run your mail-related unit and integration tests before you touch prod.
- XML parser stack (libexpat CVEs): Python updated the bundled Expat library to address CVE-2026-24515 and CVE-2026-25210, and added mitigation work tied to CVE-2025-59375. If you parse attacker-controlled XML, this one pushes you toward “patch sooner.”
- HTTP and cookie parsing hardening: Multiple modules now reject control characters in headers and fields. This can break weird edge traffic you did not know you had, especially if you proxy legacy systems.
- DoS hardening fixes: Several standard library paths reduce memory amplification and worst-case complexity. You will not “feel” these in normal traffic, but they matter under hostile inputs.
Opinion: ignore the GitHub commit count. I care about which parsers changed and which CVEs got closed, not whether the diff shows 23 commits.
How to benchmark it yourself (before and after)
On our test cluster, I run two baselines: a micro benchmark to catch interpreter-level regressions, then a workload replay to catch packaging and dependency side effects. The micro benchmark usually finishes in under 90 seconds, so there is no excuse to skip it, unless you enjoy guessing.
- Interpreter micro check: Run pyperformance before and after on the same host class. Pin CPU frequency governor if you can. Save raw JSON so you can diff it later.
- Service-level replay: Rebuild your container or venv, then replay 10 to 20 minutes of representative traffic in staging. Compare p95 and RSS deltas against the previous build.
- Extension module sanity: Import every compiled dependency at startup and fail fast. A broken wheel shows up in 30 seconds, not after your canary hits the code path at 3 a.m.
Upgrade paths that match real systems
Some folks “just bump Python” and call it done. I do not. Not on a fleet. If you run a dev box, yolo it on Friday afternoon. If you run production, canary it, because your dependency chain will surprise you at the worst time.
- Distro-managed Python (most Linux servers): Prefer your OS vendor packages so you inherit their patch pipeline and rebuilds. Then run your benchmark suite against the packaged interpreter.
- pyenv or source builds: Download the 3.12.13 source tarball, verify checksums, build, run the test suite you actually trust, then roll it into your base image or AMI.
- Containers: Bump the base image or rebuild the layer that provides Python. Keep the old image tag available for rollback, then canary 5% of traffic and watch error rate, p95, and RSS for at least one deploy window.
Breaking changes, known issues, and what I watch anyway
Upstream does not document breaking changes for 3.12.13, but “no breaking changes documented” does not mean “your app cannot break.” Control-character rejections and email parsing tweaks can surface as behavior changes in edge traffic. If you run an API gateway, watch 400/431 rates and header-related error logs.
Other stuff in this release: dependency bumps, parser hardening, the usual.
If the numbers say “flat performance” and your canary stays clean, upgrade the rest of the fleet. If your p99 jumps 8% after the rebuild, stop and figure out whether your build toolchain changed, because it probably did, and I have not tested every distro’s patch set yet, so…
🛠️ Try These Free Tools
Paste a Dockerfile for instant security and best-practice analysis.
Paste your dependency file to check for end-of-life packages.
Plan your upgrade path with breaking change warnings and step-by-step guidance.
Track These Releases